When it comes to governing risk (specifically when remediating cloud infrastructure misconfigurations) there are three common goals we hear from security leaders:
- Understand your security and compliance postures at any given time within minutes, not days.
- Automate and scale security across all cloud environments.
- Eliminate frustration and reduce the time to prioritize and remediate risk.
And these are the three most common goals we work to help you achieve at Secberus. Secberus is a cloud governance platform that relies on event-based triggers to detect any changes in your resource configuration. When changes are detected, the Secberus platform allows the risk owner to gain the context and perspective they need to take action–whether it be to edit the policy or create an exemption. The ability for the risk owner to take immediate action is allowed because all policies are written as-code and have the extensibility and customizability to adapt as needed.
There are a lot of us at Secberus that have been thinking about this problem for the last couple of years. And there’s a handful of us, including our co-founder, Fausto Lendeborg, who have lived this problem for over a decade. He, and all of us at Secberus, have a deep desire to be a part of something that is (1) truly innovative (because, it’s cool to work at the forefront of change) and (2) serves the greater community. There are a lot of smart, driven people working really hard to make this platform the best it can be so security leaders around the world can gain more confidence through a deeper understanding of what’s going on within their cloud infrastructure environments at any given time. And since we’re new(er) on the block, forgive the explicit sales pitch. Our intent is to be clear on who we are so you understand you have one more option when it comes to managing risk.
Everett Young, another co-founder and COO, is constantly talking to investors and cybersecurity greats, like Gili Lev, Sherry Ryan and Edmond Mack, to continue to validate and shape how Secberus plays a part in the cybersecurity landscape. By restructuring the landscape conversation to match what CISOs and Cloud Security Architects and their stakeholders are trying to solve for, we can help you understand what type of solution will be most beneficial.

Though simple, this revised landscape view allows you to match the risk with the intention. Is your problem that your developers don’t understand if the risks they are receiving match the intended control? Or is it that you need to answer which of your customer-facing applications may need patches due to unknown vulnerabilities? Creating a revised view of the landscape that aligns risk, role and need allows you, as the purchaser, to ask the right questions when evaluating a solution. Secberus is the right solution for prioritizing, understanding and remediating cloud infrastructure risk and not the best option, at this time, if you need a vulnerability management solution.
If you do find yourself in need of a cloud infrastructure risk solution–a cloud governance platform, rather than a CSPM, may be the way to go. A CSPM is sometimes too narrow a focus for what is needed. A cloud governance platform should help you to advance your overall cloud maturity and business continuity while also assessing, remediating and adapting both security and compliance policies. This kind of solution must also leverage Policy-as-Code.
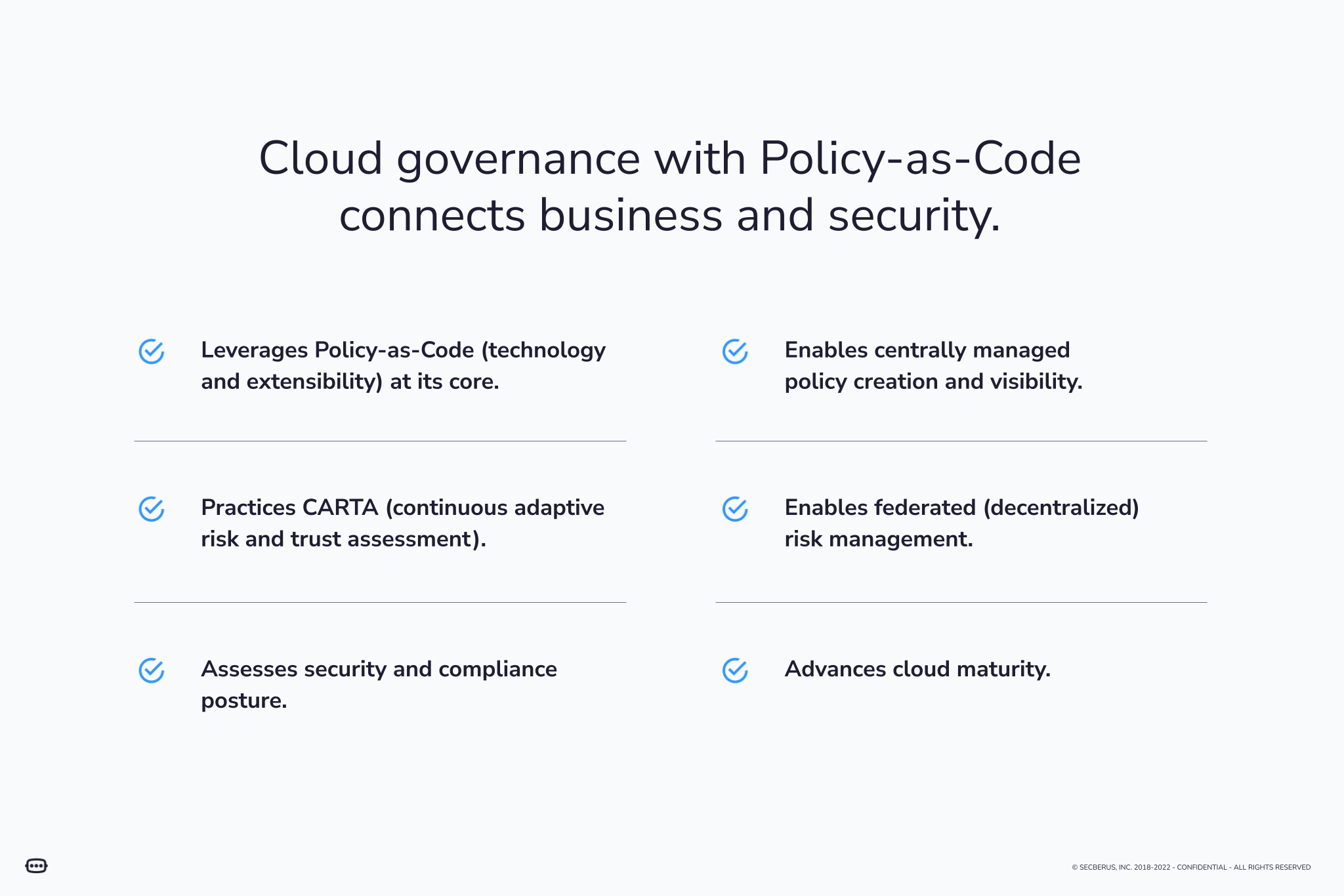
In order to practice cloud governance in a way that realizes the above benefits you need three things. The 1-2-3 punch of cloud governance, if you will.
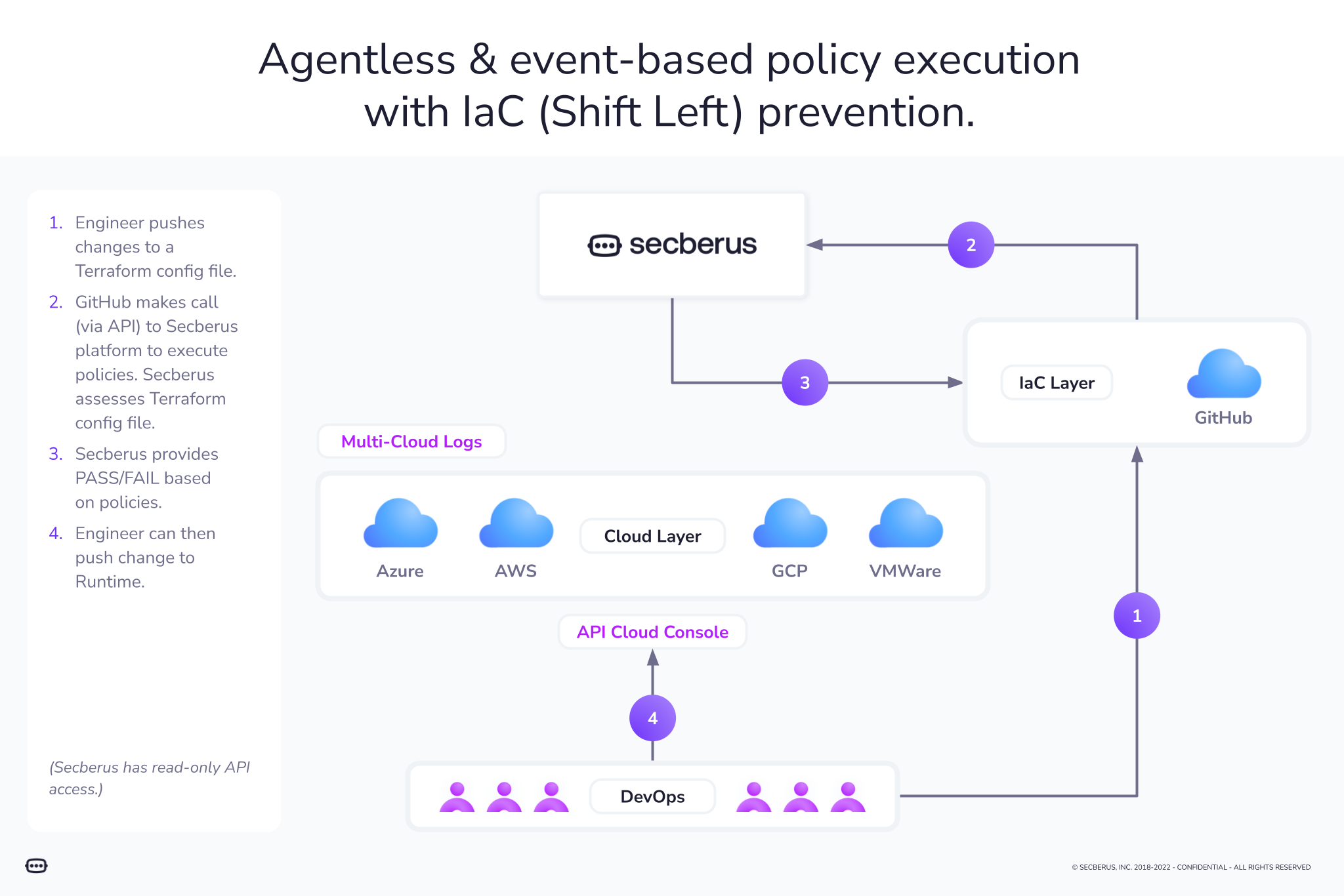
Punch 1: Event-based triggering
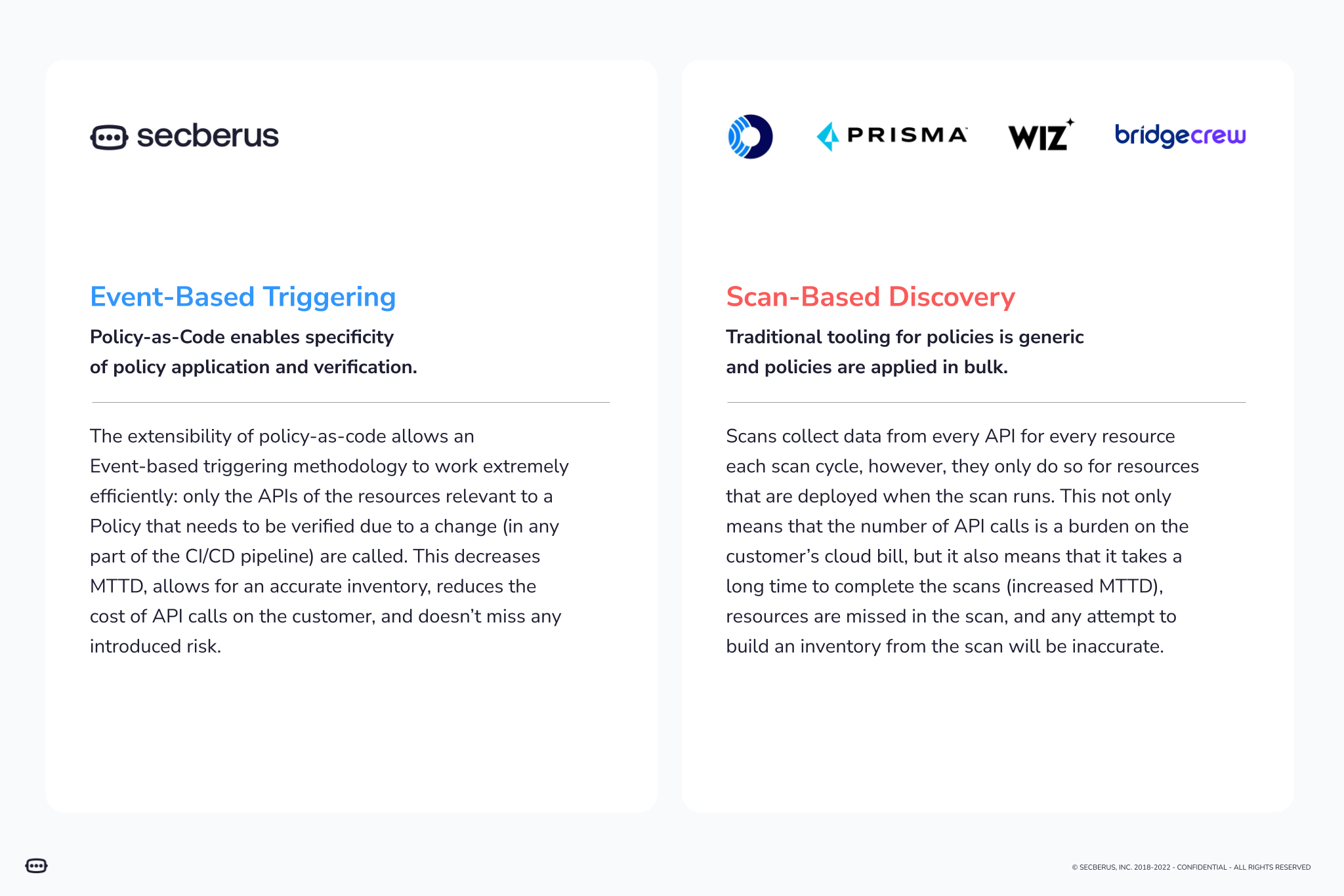
There is a time and a place for both types of discovery. The point is if you have a need or desire to start assessing risk in near real-time and you have an appetite to change the security culture within your organization then you are in a position to consider what an event-based triggering solution can bring to your table. Event-based triggering will give your security leaders the context to understand and communicate cloud infrastructure risk faster and with higher real-time accuracy. Having this power will inevitably begin to shift the culture of security within your organization.
Punch 2: Policy-as-Code as a built-in core platform technology
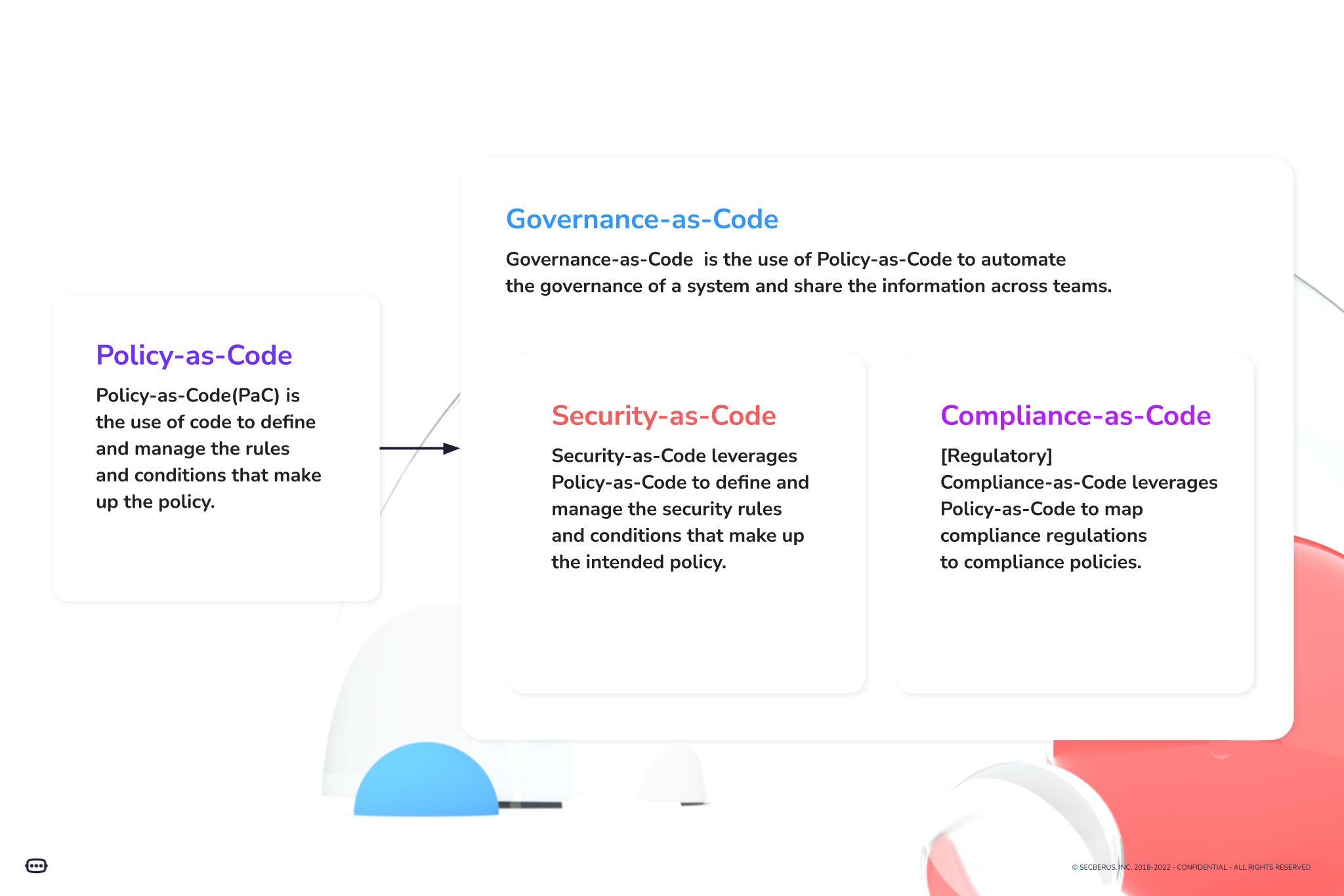
Think of Policy-as-Code as the lifeforce of cloud governance. Without leveraging an as-Code approach, you can not reap the benefits of scale or prioritization of risk.
Whether it’s policy, governance, security, or any other business activity, anything “as-Code” encodes human capabilities and activities in a programming language. Doing so is powerful because it transforms these activities into technological capabilities that are editable and scalable beyond human capacities.
“As-Code” is what makes the cloud (and cloud security) so game-changing, because it:
- Enables you to embrace exponential data growth.
- Enables consistency.
- Enables automation.
- Empowers you to build replicable libraries of code around key activities like configuration and policy-enforcement.
- Creates potential for “immutable infrastructure” that is deployed and maintained in code without manual intervention, which means less scope for error and therefore less chance of risk.
Here’s an example of how as-Code works:
Punch 3: Federated risk management
We have heard loud and clear that you want to give your DevOps teams the visibility to enable them to secure their applications and not get frustrated or give up in the process. Hopefully, you may be starting to see how a cloud governance platform can help eliminate this pain. With event-based triggering, we see that changes are detected in real-time. With Policy-as-Code you’re granted the ability to adapt, customize and scale your policies with relative ease. And with the addition of this third punch, federated risk management, you are granted permission to provide risk owners with the appropriate context to remediate risk on the spot. And because risk owners are able to remediate in real-time (including writing exceptions, if applicable) and have those changes applied at scale, alert fatigue becomes a thing of the past.
The combination of federated risk management and centralized cloud security governance provides the best user experience for your organization. Strategies for both role-based access control and attribute-based access control must be thought through and applied in order to take full advantage of this offering. As soon as you understand the roles and access privileges you want to provide and to whom, the more you are ready and able to advance your cloud maturity and help reign in the complexity of your cloud security environment.
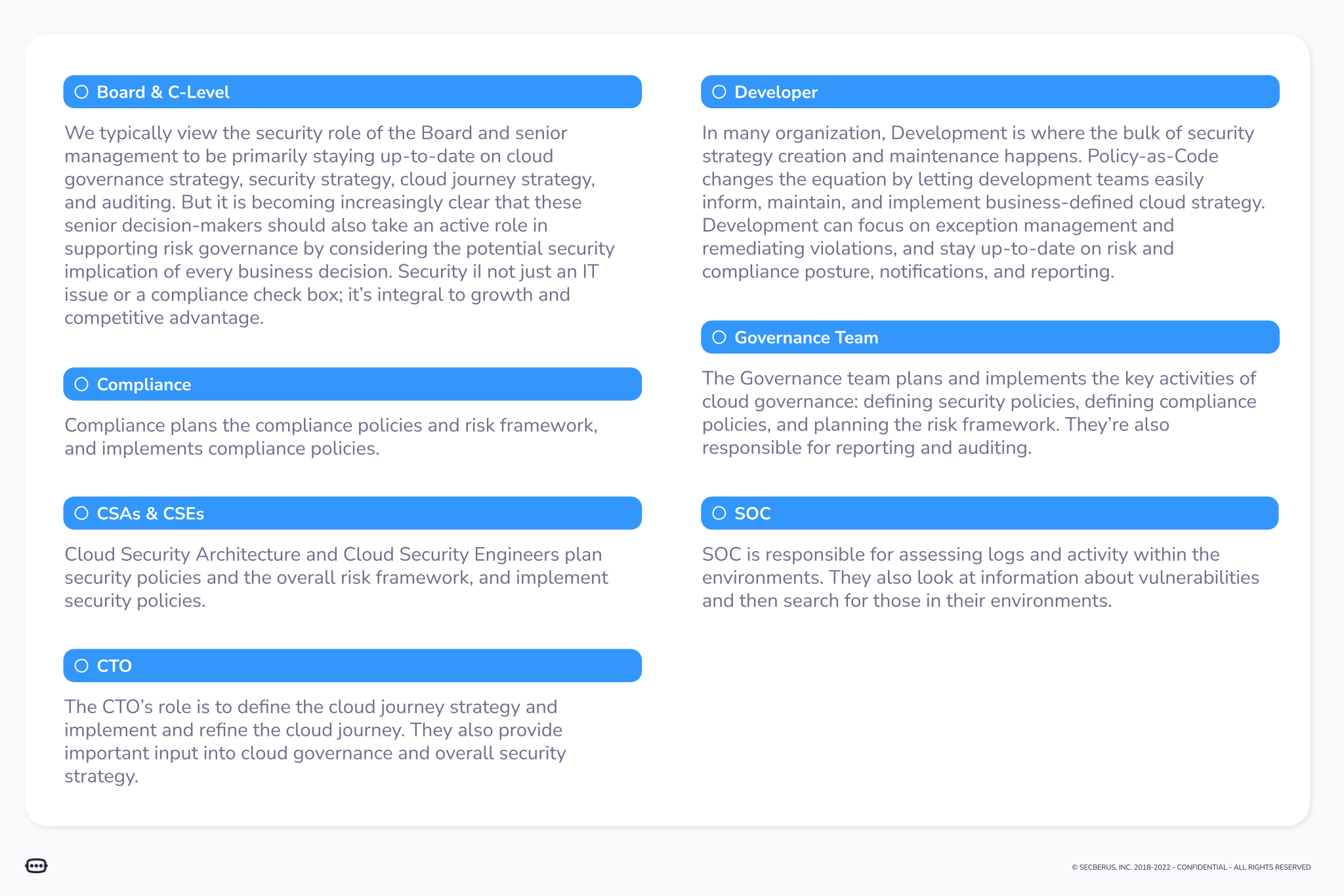
If you’re serious about evaluating cloud governance, here is a sample of how some of the roles and responsibilities may start to shift within your organization:
Secberus is serious about helping multi-cloud enterprises tackle some of the biggest pains associated with cloud security risk management today. We are committed to partnering with our customers to enable the change you need to make your security practice as valuable, informative and business-friendly as possible.
If you’re looking to implement this kind of change yet worried about implementing a new process, especially in light of a recession, your next step may be to better understand the total cost and benefits of cloud risk. (Not ready to fill in our form, get the ungated copy here.)