Introducing ABAC
Attribute-based access control (ABAC) is an access control method that evaluates characteristics called “attributes,” such as assigned users, objects, or sets of policies to determine access. It’s well-known that ABAC provides more flexibility and agility to access control. The White House recently released a memorandum recommending ABAC be a part of the zero trust strategy. The memorandum states, “A zero trust architecture should incorporate more granularly and dynamically defined permissions, as attribute-based access control (ABAC) is designed to do.”
ABAC assesses a user’s attributes at the time of access, making an informed decision about whether to allow or deny access. Access policies in an ABAC system determine the combinations of the attributes (i.e., users, environment, and resources) required to perform a particular action.
The main categories of attributes are:
- User Attributes – describes the information about the user trying to gain access, including name, title, and permissions level.
- Environment attributes – describes the attribute that contextualizes the access attempt, for example, location, time, or device.
- Resource attributes - describes the resource request for access.
ABAC provides centralized control, flexibility, and fine-grained access control to handle permissions for each attribute category. For example, David Cohen is a DevOps engineer at ACME. With ABAC in place, he can identify with these attributes:
- Active employee
- Part of the IT organization
- Approved access by the CISO
David Cohen meets the above attributes and is therefore granted access to the data he needs.
This makes ABAC a more strategic and flexible approach that lets you use granular control by leveraging multiple attributes from different areas of the organization. ABAC allows organizations to manage their resources at scale by enabling them to implement complex access control policies to meet their unique business needs.
ABAC in Secberus
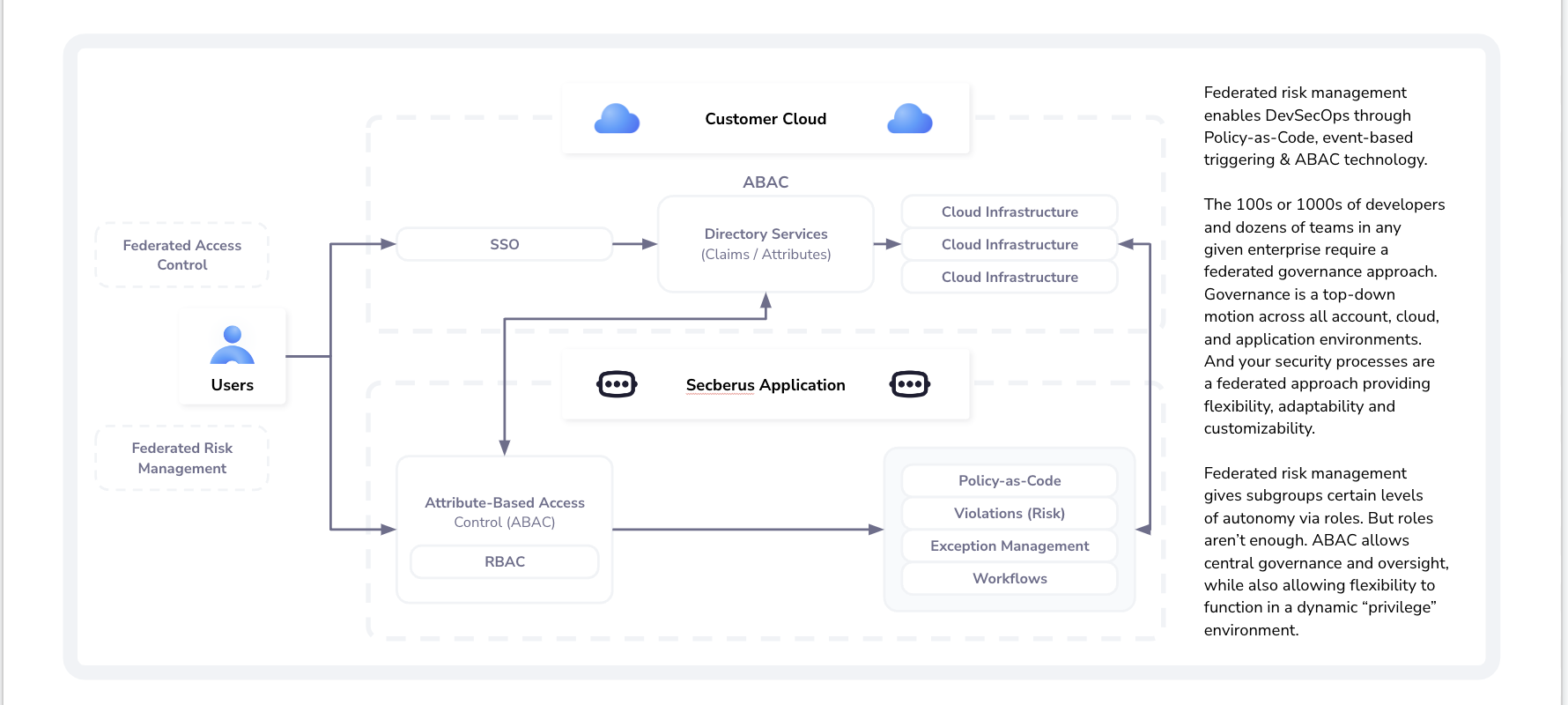
One of the most significant advantages of ABAC is that it allows federated risk management to excel within an enterprise. Security leaders are given permission to provide their team with the right context to remediate risks on the spot. And with this ability, combined with our Policy-as-code technology, which prioritizes risk, alert fatigue becomes a thing of the past.
ABAC also allows administrators the ability to implement access restrictions, providing the right context for security and compliance decisions. As a result, security leaders and DevOps teams will have the ability to view and manage security risk within their own dashboard. This, correspondingly improves the organization’s security posture, productivity, and collaboration.
In addition, ABAC lets organizations keep their data, network, and resources secure by granting or denying access. All-access requests are processed and evaluated in real-time by the authorization engine based on the user or agent’s attributes.
How to Implement in Secberus?
Let’s take a step-by-step look at how to set up and manage users in Secberus.
With Secberus’ ABAC you can use our predefined roles that can be assigned to users within organizations or create your own custom roles to limit user access and privileges for specific resources based on a wide range of attributes. Each user can be assigned multiple roles within each organization.
Creating Custom Roles:
To create a custom role, include the name of the role, and a short description, and then select one or more access policies that define the privileges for the role.
Creating Access Policies:
Custom access policies can be created by following a simple syntax. Policies will be composed of two sections: Action and Condition. Permissions are purely additive (there are no “deny” rules).
Final Thoughts
Access management is a crucial component for modern enterprises due to the change in the digital landscape. Enterprises need a robust and versatile solution that can help govern their resources, enabling every stakeholder (i.e., security teams, architects, and DevOps) to focus on development and collaboration.
Secberus’ ABAC provides federated risk management across your enterprise’s multi-cloud environment. It allows you to implement and scale an access management strategy by standardizing roles and fine-grained authorization. This increases organizational agility and enables the business to respond to changes in business and regulatory requirements.
In the future, we plan to add more ABAC support in Secberus.

